New security features for your Stripe account
Today, we’re launching two additional features to improve the security of your Stripe account: an option to use hardware tokens for two-step authentication and the ability to create API keys with restricted access and granular permissions.
Two-step authentication with hardware tokens
We first introduced two-step authentication for Stripe accounts back in 2012. Now, in addition to SMS or using Google Authenticator, you can also register a physical security key to approve logins to your Stripe account. We support any device using the Universal 2nd Factor (U2F) standard hosted by the FIDO Alliance. You can read more about the devices and browsers we support; of note, a single hardware key can be registered for two-step authentication with multiple services like AWS, Google, GitHub, and more.
We recommend using a hardware key to protect your Stripe account because they are designed to be resistant to phishing attacks. A U2F key requires physical access to the hardware device, not just access to your password. Unlike two-step authentication that uses SMS or Google Authenticator, you can't be tricked into entering a pin on the wrong website. In addition, tapping the device is faster than waiting for an SMS code and typing it in.
When you’re ready, you can register a device from your Dashboard settings. Note that you’ll need to enable at least one other two-step authentication method as a backup option before you can add your security key.
Restricted access API keys
We’ve added the ability for businesses to generate multiple API keys, allowing developers to safely grant programmatic access to Stripe accounts while precisely defining the scope of each API key; these keys can also be revoked at any time.
We’ve heard from many of our users—from startups to public companies—that their engineering teams increasingly rely on multiple microservices to interact with and use Stripe’s API. You can now restrict each of these services to the minimum required set of permissions to reduce risk. For example, a data analytics service may be allowed to only read charges on a Stripe account, or the backend for customer support software may be able to exclusively issue refunds, but not alter customer information. Businesses can also use this feature to define restricted access and safely share data when working with third-party partners.
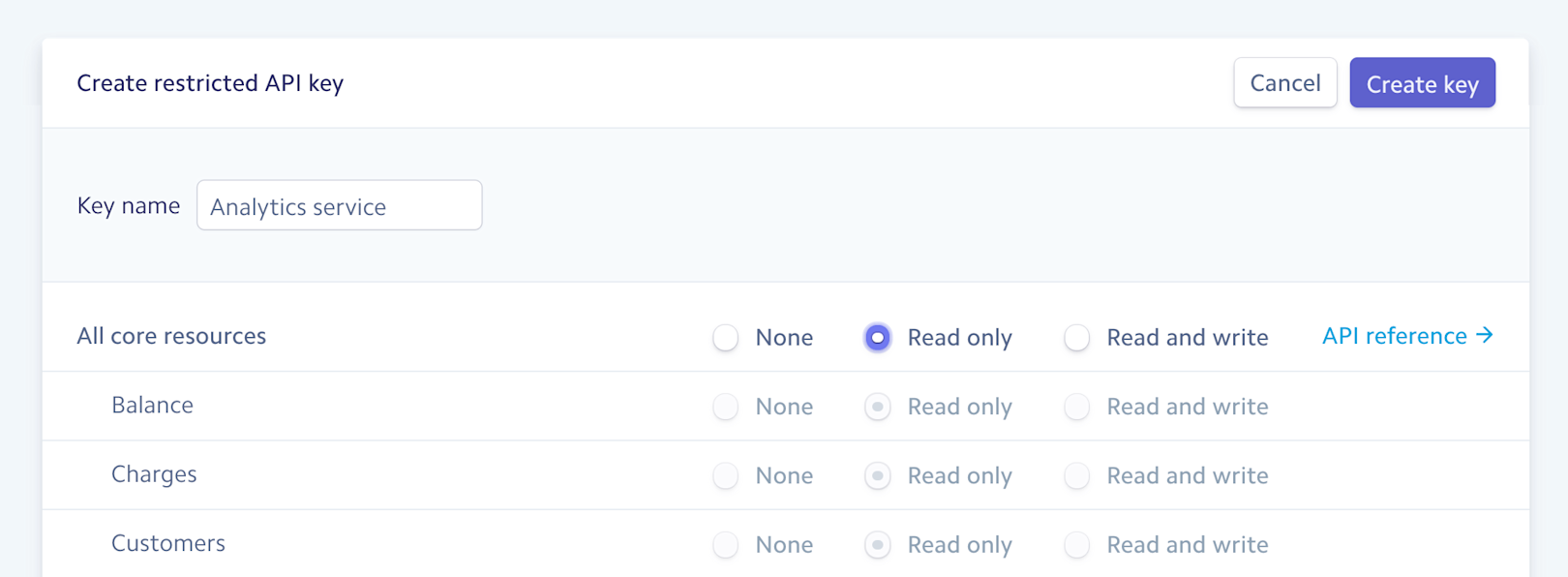
You can generate an API key with restricted access from the Dashboard today.
We hope these features help your business keep your Stripe account safe. You can also check out our security guide to learn about more ways to keep your Stripe integration secure.

